Recently there was a huge hue and cry in May when the WannaCry ransomware attacked the worldwide cybersecurity creating havoc and jeopardizing the function of close to some two and a half million computers in about 150 countries. Its prime target was computers using Microsoft Operating System. Now, the intention of informing you all this is that if you are using an Android or iOS phone, please don’t be under the impression that you are within the ages of a safe umbrella.
Today, when we have the luxury of accessing the internet on our mobile phones, it has become utmost important to guard the devices with the shield of protection. You are already aware of the fact that not all websites are considered safe for visiting. The same can be said about mobile apps as well.
According to the recent survey, it was found that Smartphone owners are using average 30 applications per month. But are you sure that they are 100% hack proof? No, you cannot bet on that. Even a trifling issue can prove to be quite expensive and you have to pay a heavy penalty for it. And beware that nowadays the hackers have become smarter and so you need to be very careful when browsing the internet on mobile devices.
In this article, you will learn the best five techniques for app security and safeguard your confidential data from getting hacked.
1. Providing Security with Multifactor Authentication
Multifactor Authentication or MFA, in short, is indeed a great in order to combat hacking and cybercrime. The multinational companies offered this facility to their employees but today social media giants such as the Twitter is to offering the same to its users.
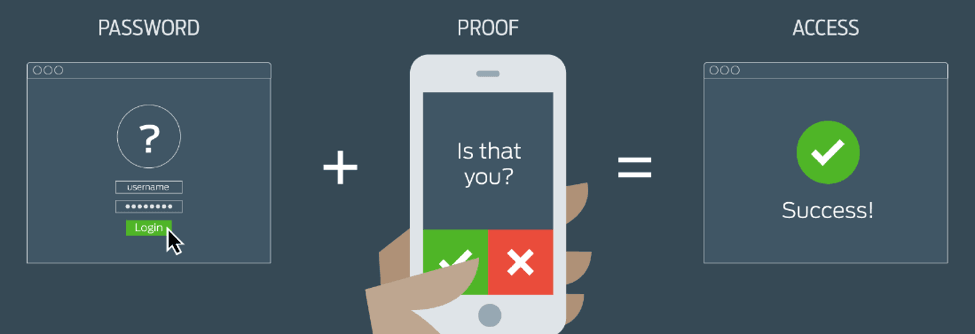
Now, you must know how this procedure works? Once you are logging in with your username and password, you will have to show that you own a mobile handset too with a different account linked with the user account. This is the additional security which will protect your secured information even if the username or password has been stolen. It will take you less than 10 minutes to set the rules; thereby enabling the multifactor authentication to get activated with the help of Duo Security or Google Authentication. After login, the MFA will ask to validate with your second device and if you are logging for the first time, they will have to get your device registered with an MFA provider.
Setting the rule is as easy as eating your favourite dish. Once you choose your provider, your next job is to configure the associated rule. One of the biggest advantages of having the rule is that it allows you to configure MFA under various conditions such as geographical location or change of place, type of network or type of device used.
And to provide this kind of security, what needs to be done is write little extra conditional logic in JavaScript. You can either activate MFA as soon as the user logs when you smell something foul. Moreover, you also understand the burden of MFA.
For example, every time you login into your Gmail account from a different device, the Gmail team sends you an email with warning information that your account was logged in from some other device. It also encourages users to keep on changing their passwords at regular intervals.
2. Be Cautious of Malicious Codes
The malignant codes and mobile malware has certainly become one of the biggest challenges for cybersecurity engineers. According to the latest data, approximately about 36.5 million Android devices reportedly infected with malware. Let’s now look into how shrewd these cybercriminals have to become and how there is choosing their soft target.
The cyber attackers in the first place attain a duplicate copy of the application and then reverse engineer it. Then these most commonly used or popular mobile apps are duplicated or they are launched in the pirated version to be released in the market. These are better known as the ‘Rouge Apps’, which contain the malware codes. They are mostly launched on third-party app stores that are not authenticated. These fake or pirated apps are promoted amongst the users, alluring them to install it.
It is important to provide the app developer to beware of such malicious codes and also take note of the loopholes in protecting their apps. As for the users, they should be careful before installing any app into their mobile.
3. Calculation of User Fraud Score
Nowadays, E-commerce websites have become intensely popular and as such is regarded as one of the frequently visited online marketplaces. However, if you are an owner to one of these marketplaces, such as Go Local Classified, it is your liability to provide a secured and safe environment to all your buyers and site visitors.
The rulebook states that you need to calculate a fraud score for every user based on their email id and IP address. This will help you identify whether the user is real or fraud. But how will you do this? The cloud service can be of great help in this regard. What it does is it takes a cumulative data from offline social media authentication as well as web data.
The data will help in securing your app as well as you can also keep a vigil on your users by the high fraud scores. You can ask them to verify their identity before they deal with the other users. Moreover, it is always advisable to keep your user information in your database to avoid hackers entering the site.
4. The Android Keychain and iCloud Keychain
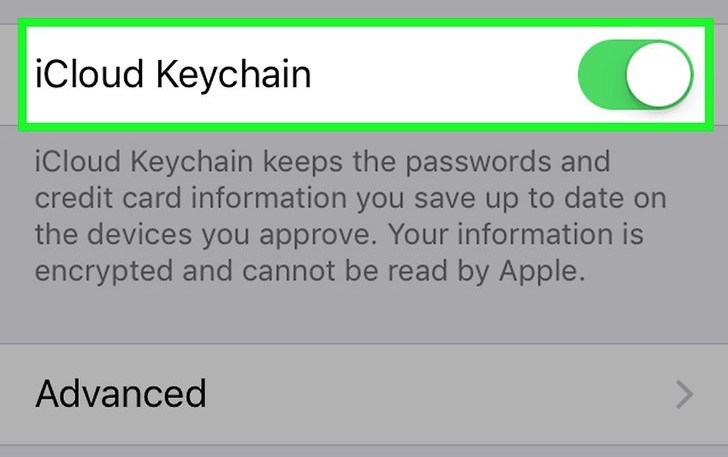
A keychain can be defined as one of the optimal highly protected storehouses which contain all the confidential information that includes usernames, passwords and other such classified data all at one place. The keychain is developed by the different operating systems providers such as the Android and the iOS. It is much safer to keep all data in keychain instead of p-list and NSUserDefaults. Another plus point of using a keychain is that you don’t have to log in every time when you want to open the application.
5. Device Security and Encryption
So till now, your focus was on strengthening the security of the mobile application, but did you think over the device? Yes, the device’s security is equally important and it simply cannot be neglected. There is every change of the app coming under the scanner if it has a jailbroken or rooted device. Therefore, you have to tighten the screws and give the device an unmatched protection from beneath. The app sandbox must be under a strict vigil because rooting or jailbreaking will lead to an increase in insecure data and weaken the security model.
Encryption in simple language means to convert any data or confidential information into codes or cypher which is unreadable with the help of some special algorithm keys. It is one of the best-secured ways to protect your data.
Conclusion
Well, although the blog has highlighted the five optimal methods that you can implement to safeguard your data, the list does not end here. There are various other techniques that can be employed for data security. You can opt for email verification, keep updating your software, restrict intruders into your phone and so on. Always keep in mind that in order to outdo cyber criminals, you need to be one step ahead of their game plan.
Jassica is an Editor of App Story and. For the last seven years, she has been contributing for leading mobile app development company Atlanta and online publications, including, App Story & CEO Interview Platform, Dataflow, Dzone, B2C etc. At the workplace, she is admired for her team management skill. She leads a team of 20-something creative writers and designers.
